Not all Linux distributions are created equal. When choosing a Linux distribution, there are several things you need to keep in mind.
Release Cycle
You should choose a distribution which stays close to the stable upstream software releases, typically rolling release distributions. This is because frozen release cycle distributions often don’t update package versions and fall behind on security updates.
For frozen distributions, package maintainers are expected to backport patches to fix vulnerabilities (Debian is one such example) rather than bump the software to the “next version” released by the upstream developer. Some security fixes do not receive a CVE (particularly less popular software) at all and therefore do not make it into the distribution with this patching model. As a result minor security fixes are sometimes held back until the next major release.
In fact, in certain cases, there have been vulnerabilities introduced by Debian because of their patching process. Bug 1633467 and DSA-1571 are examples of this.
The practice of holding packages back and applying interim patches is generally not a good idea, as it diverges from the way the developer might have intended the software to work. Richard Brown has a presentation about this:
Even if you are worried about the stability of the system because of regularly updated packages (which you shouldn’t be), it makes more sense to use a system which you can safely update and rollback instead of an outdated distribution partially made up of unreliable backport packages without an easy rollback mechanism in case something goes wrong like Debian.
Arch-based Distributions
Arch Linux has very up-to-date packages with minimal downstream patching. That being said, Arch-based distributions are not recommended for those new to Linux, regardless of the distribution. Arch does not have an distribution update mechanism for the underlying software choices. As a result, you have to stay aware with current trends and adopt technologies as they supersede older practices on your own.
For a secure system, you are also expected to have sufficient Linux knowledge to properly set up security for your system such as adopting a mandatory access control system, setting up kernel module blacklists, hardening boot parameters, manipulating sysctl parameters, and knowing what components you need such as Polkit.
If you are experienced with Linux and wish to use an Arch-based distribution, you should use Arch Linux proper, not any of its derivatives. Downstream distributions may come with bad practices like holding back packages (as is the case with Manjaro), blindly building packages from the AUR (as is the case with Garuda and its Chaotic-AUR repository), or just not setting up the basics such as mandatory access control or firewalls.
“Security-focused” Distributions
There is often some confusion about “security-focused” distributions and “pentesting” distributions. A quick search for “the most secure Linux distribution” will often give results like Kali Linux, Black Arch and Parrot OS. These distributions are offensive penetration testing distributions that bundle tools for testing other systems. They don’t include any “extra security” or defensive mitigations intended for regular use.
Linux-libre Kernel and “Libre” Distributions
Do not use the Linux-libre kernel, since it removes security mitigations and suppresses kernel warnings about vulnerable microcode for ideological reasons.
If you want to use one of these distributions for reasons other than ideology, you should make sure that they there is a way to easily obtain, install, and update a proper kernel and missing firmware. For example, if you are looking to use GUIX, you should absolutely use something like the Nonguix repository and get all of the fixes as mentioned above.
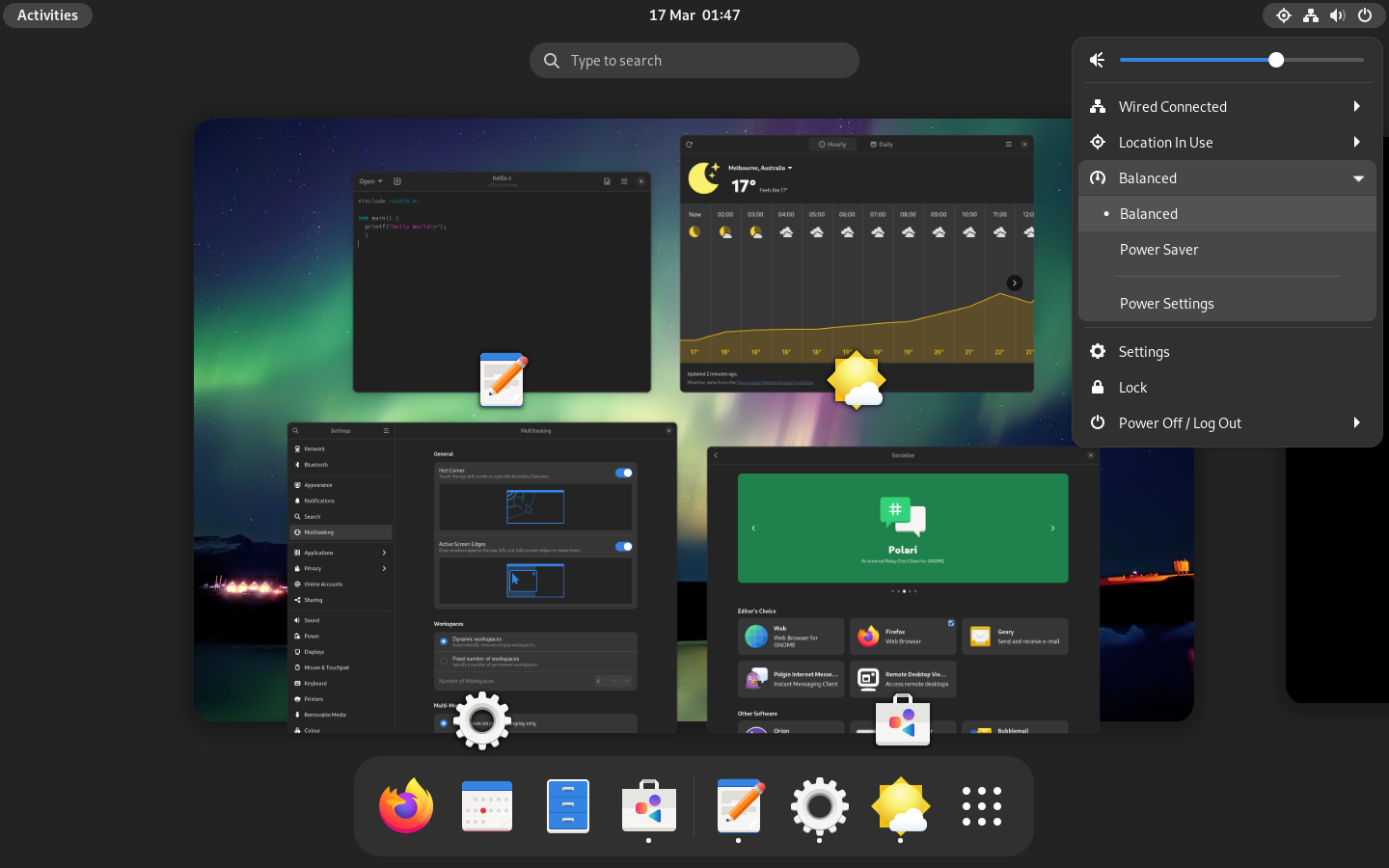
Desktop Environments
Consider using GNOME as your desktop environment. It supports Wayland, a display protocol developed with security in mind, and implements permission control for privileged Wayland protocols like screencopy. There are other desktop environments and window managers with Wayland support, but we are not aware of any permission control implemented by them. One caveat with GNOME is that it is written in unsafe languages, but we think the trade off for permission control is well worth it.
Wayland’s predecessor, X11, does not support GUI isolation, allowing all windows to record screen, log and inject inputs in other windows, making any attempt at sandboxing futile. While there are options to run nested X11 sessions such as Xpra or Xephyr, they often come with negative performance consequences, are not convenient to set up, and are not preferable to Wayland. You should avoid desktop environments and window managers which only support X11.
Recommended Distributions
Here is a quick, non-authoritative list of distributions we recommend over others:
Fedora Workstation
Fedora Workstation is a great general-purpose Linux distribution, especially for those who are new to Linux. It is a semi-rolling release distribution. While some packages like GNOME are frozen until the next Fedora release, most packages (including the kernel) are updated frequently throughout the lifespan of the release. Each Fedora release is supported for one year, with a new version released every 6 months. The distribution takes an “upstream first” approach and ship packages with minimal downstream patching, and the patches are done in a sensible manner which does not unexpectedly break functionalities unlike Debian.
With that, Fedora generally adopts newer technologies before other distributions e.g., Wayland and PipeWire. These new technologies often come with improvements in security, privacy, and usability in general.
Fedora’s package manager, dnf, has a great rollback and undo feature that is generally missing from other package managers. You can read more about it on Red Hat’s documentation.
Fedora Atomic Desktops
Fedora Atomic Desktops are immutable variants of Fedora with a strong focus on container workflows. While they do not provide security benefits over Fedora, they have a much more reliable update mechanism. Unlike traditional Linux where packages are updated one by one, Atomic Desktops will download a whole new OS image first before rebooting to switch over to the new image. The system cannot fail in the middle of an update, and should something be wrong with the new image, it only takes one reboot to return the system to its previous state. Should you feel the dnf rollback mechanism isn’t enough, we recommend giving Fedora Atomic Desktops a try.
Adam Šamalík has a presentation with rpm-ostree in action:
One caveat with Fedora Atomic Desktops is that rpm-ostree currently has a hard dependency on grub and does not support Unified Kernel Images. The consequence of this is that unlike Fedora Workstation, it is not possible to set up a Fedora Atomic system with meaningful Secure Boot to resist physical tampering.
SecureBlue
SecureBlue provides hardened operating system images based on Fedora Atomic Desktops. While they do additional parties of trust (SecureBlue, GitHub infrastructure, BlueBuild, Negativo, etc), their images are substantially hardened and not easily replicated by hand. There are several very interesting packages maintained by SecureBlue as well:
- Trivalent, a hardened chromium desktop build with patches from GrapheneOS’s Vanadium.
- Hardened Malloc. SecureBlue packages GrapheneOS’s memory allocator and enables it system wide, including for Flatpak applications.
openSUSE Aeon
Fedora Atomic Desktop’s European counterpart. openSUSE Aeon is a rolling release, fast updating distributions with transactional updates using Btrfs and Snapper.
Aeon has a relatively small set of base packages (thus lowering the attack surface) and mounts the running BTRFS subvolume as read-only. Updates are applied package by package to a new BTRFS snapshot before the system is rebooted to the new subvolume. This allows the rollback process to be relatively easy just like on Fedora Atomic Desktops.
Whonix
Whonix is a distribution focused on anonymity based on Kicksecure. It is meant to run as two virtual machines: a “Workstation” and a Tor “Gateway.” All communications from the Workstation must go through the Tor gateway. This means that even if the Workstation is compromised by malware of some kind, the true IP address remains hidden. It is currently the best solution that I know of if your threat model requires anonymity.
Some of its features include Tor Stream Isolation, keystroke anonymization, boot clock randomization, encrypted swap, hardened boot parameters, and hardened kernel settings. One downside of Whonix is that it still inherits outdated packages with lots of downstream patching from Debian. It would be better if Whonix gets reimplemented on top of a more sensible base like SecureBlue, although no such system publicly exists yet.
Although Whonix is best used in conjunction with Qubes, Qubes-Whonix has various disadvantages when compared to other hypervisors.